Recently, internal chat logs and operational details of the BlackBasta group were leaked online. According to reports, these leaks revealed how the group operates, including their communication methods, target selection, and ransom negotiation tactics. The leaked information provides valuable insights into the group’s structure and strategies, potentially aiding law enforcement and cybersecurity professionals in combating their activities. The leaked archive contains messages exchanged in Black Basta’s internal chat rooms between September 18, 2023, and September 28, 2024.
Impact on Organizations, Governments, and the Public
Organizations: The leak highlights the ongoing threat posed by BlackBasta. Companies targeted by the group face significant financial losses, operational disruptions, and reputational damage. The exposure of internal chat logs may help organizations better understand the group’s tactics and improve their defenses.
Governments: The leak underscores the need for stronger cybersecurity regulations and international cooperation to tackle ransomware groups. Governments may use the leaked information to track down members of the group and disrupt their operations.
Public: For individuals, the leak serves as a reminder of the risks posed by ransomware attacks. If organizations holding personal data are compromised, individuals could face identity theft, financial fraud, and other privacy violations.
Broader Implications
The leak of BlackBasta’s internal communications is a rare but significant event in the fight against cybercrime. It provides an opportunity for cybersecurity experts to analyze the group’s methods and develop better countermeasures. However, it also shows how sophisticated and organized ransomware groups have become, emphasizing the need for continuous vigilance and investment in cybersecurity.
In summary, BlackBasta remains a serious threat, but the recent leak of their internal operations offers a chance to better understand and combat their activities. This event serves as a wake-up call for organizations, governments, and individuals to prioritize cybersecurity and protect against future attacks.
Translation: A place to discuss the most important news about Black Basta, one of the largest ransomware groups in Russia, which recently hacked domestic banks. With such cases, you can say they crossed the line, so we are dedicated to uncovering the truth and investigating Black Basta’s next steps. Here you can find information you can trust and read all the most important information in one channel.
Our exclusive access provides thorough, objective, and reliable information, available at this link:
/file/KiIBDArA#IupYaWMdnin123ntH2SjUtQ5TxhTBNx48t_ABZmjONg (deleted)
Translation:
I contacted members of the BlackBasta group as part of my research.
Here are the specific questions I asked them, but they declined to comment.
1. Lapa, one of the main administrators of BlackBasta, is constantly busy with administrative tasks.
2. Despite holding this high-trust position, he is often insulted by his boss, who constantly demands that “everything be changed.”
3. … he experiences a lot of stress due to his role but receives significantly less compensation than others in the group.
4. … ransom payments are likely an additional source of income to support his family during these difficult times.
5. … under his administration, BlackBasta carried out a ‘brute force’ attack on the infrastructure of some Russian banks. It seems that no measures have been taken so far by law enforcement, but it can be concluded that this situation could present a serious problem and provoke a response from these authorities.
1. Cortes was associated with the Qakbot group, which…
2. … had some dealings with Americans last year, which undoubtedly could have attracted the attention of intelligence agencies.
3. When BlackBasta carried out these attacks on Russian banks, Cortes distanced himself from these actions, perhaps surprised that this Russian group conducted targeted attacks against its own country, and this is likely why Qakbot, presumably, did not participate in the attacks against Russia.
1. YY is one of the main administrators of BlackBasta, and it seems that he is very busy with support tasks and receives a good salary.
2. The arrest of the leader of BlackBasta poses significant risks for the remaining members of the group…
3. … it turned out that the personal financial gains of Oleg, the boss of this group, drive the operations, without considering the interests of the team.
4. … under his administration, BlackBasta carried out a ‘brute force’ attack on the infrastructure of some Russian banks. It seems that no measures have been taken so far by law enforcement, but it can be concluded that this situation could present a serious problem and provoke a response from these authorities.
1. … when Trump and Bio worked together in Conti, disputes over compensation issues were not uncommon.
2. Naturally, Bio is paid more in his current position so that he can continue to bear such a high level of risk.
3. … he changed his nickname from “bio” to “pumba” when he worked in Conti, but has now returned to his old nickname in BlackBasta. Therefore, his reputation in BlackBasta should not be associated with the nickname “pumba.”
4. … members of the BlackBasta group were likely concerned about his recent arrest and treatment by the police.
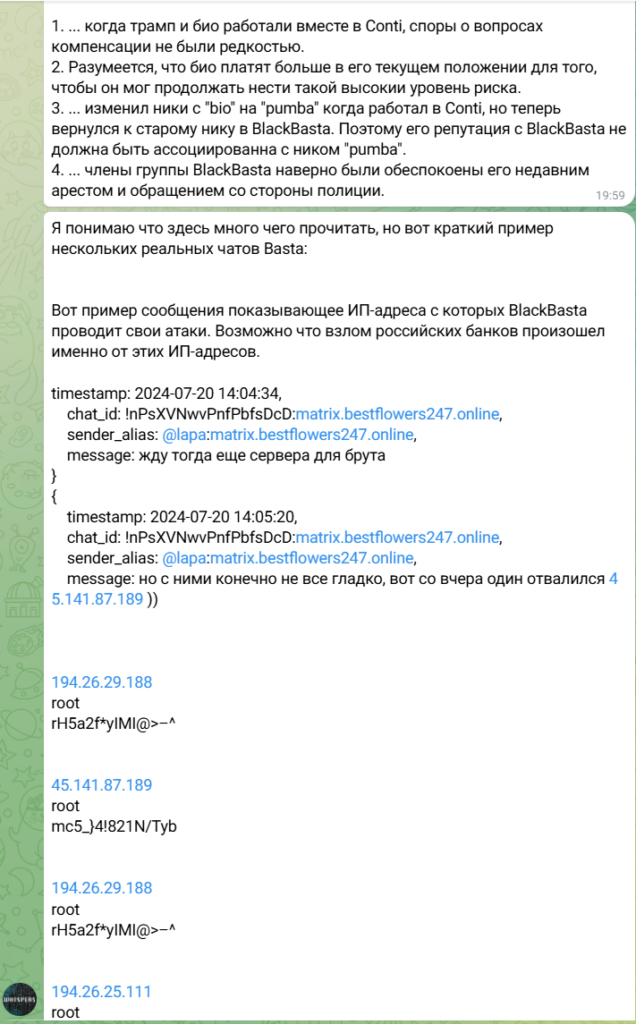
I understand that there is a lot to read here, but here is a brief example of some real Basta chats:
Here is an example of a message showing the IP addresses from which BlackBasta conducts its attacks. It is possible that the hacking of Russian banks occurred from these IP addresses.
timestamp: 2024-07-20 14:04:34,
chat_id: !nPsXVNwvPnfPbfsDcD:
[…]
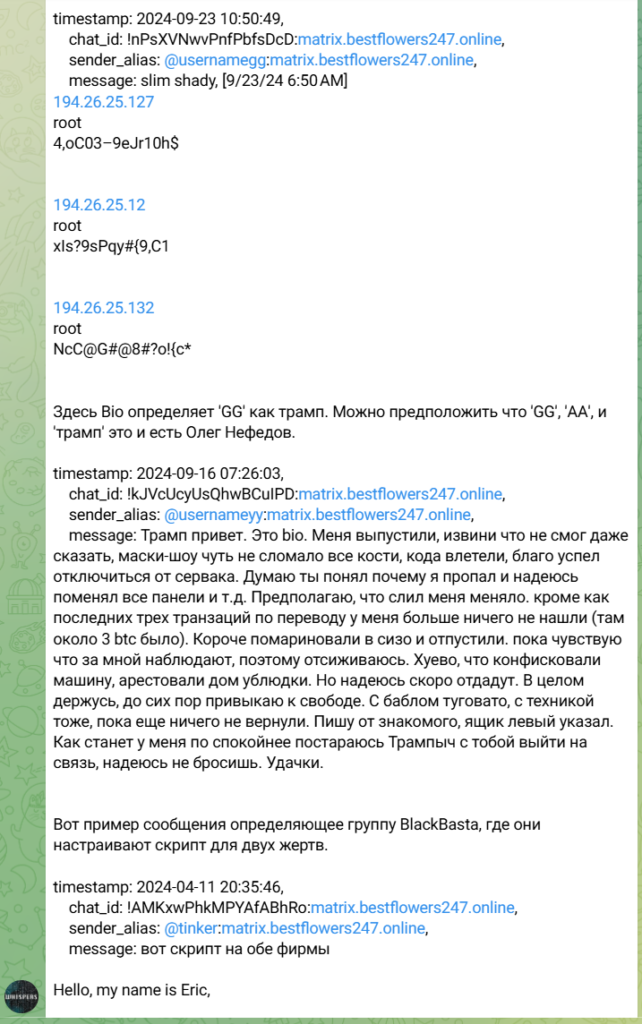
Here, Bio identifies ‘GG’ as Trump. It can be assumed that ‘GG’, ‘AA’, and ‘Trump’ are Oleg Nefedov.
timestamp: 2024-09-16 07:26:03,
chat_id: !kJVcUcyUsQhwBCuIPD:matrix .
,
sender_alias: @usernameyy:matrix .
,
message: Trump, hello. This is Bio. They released me, sorry I couldn’t even let you know. The masked show almost broke all my bones when they busted in, but luckily I managed to disconnect from the server. I think you understand why I disappeared and hopefully you’ve changed all the panels, etc. I suspect the exchanger ratted me out. They didn’t find anything on me except for the last three transfer transactions (there were about 3 BTC there). Anyway, they kept me in the detention center for a while and then let me go. For now, I feel like I’m being watched, so I’m laying low. It sucks that they confiscated my car and seized the house, those bastards. But I hope they’ll return it soon. Overall, I’m holding up, still getting used to freedom. Money is tight, and so is tech—they haven’t returned anything yet. I’m writing from a friend’s account, using a fake email. Once things calm down a bit, I’ll try to reach out to you, Trumpych, I hope you won’t abandon me. Good luck.
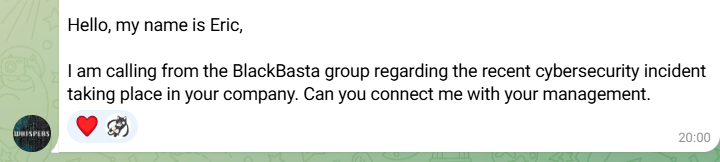
Here is an example of a message defining the BlackBasta group, where they are setting up a script for two victims.
timestamp: 2024-04-11 20:35:46,
chat_id: !AMKxwPhkMPYAfABhRo:matrix .
,
sender_alias: @tinker:matrix .
,
message: here’s the script for both firms
Hello, my name is Eric, I am calling from the BlackBasta group regarding the recent cybersecurity incident taking place in your company. Can you connect me with your management.
The telegram account is Шепот Басты
Indicators of Compromise (IOCs)
Summary of IoCs
IP Addresses: 194.26.29.188, 45.141.87.189, 194.26.25.111, 194.26.25.127, 194.26.25.12, 194.26.25.132
Domains:
matrix.bestflowers247.onlineUsernames:
@lapa,@usernamegg,@usernameyy,@tinkerCryptocurrency: 3 BTC transactions
Attack Techniques: Brute-force attacks, VPN/proxy usage, malicious scripts
Internal Conflicts: Payment disputes, leadership issues, internal leaks
These IoCs can be used for threat hunting, monitoring, and improving defensive measures against BlackBasta’s activities.
Analysis
1. IP Addresses
The following IP addresses were identified as being used by BlackBasta for their attacks, particularly against Russian banks:
- 194.26.29.188
Credentials:
root/rH5a2f*ylMl@>--^
- 45.141.87.189
Credentials:
root/mc5_j4l821N/Tyb
- 194.26.25.111
Credentials:
root/)xvMZg48n6bX}5A
- 194.26.25.127
Credentials:
root/4,oC03–9eJr10h$
- 194.26.25.12
Credentials:
root/xls?9sPqy#(9,C1
- 194.26.25.132
Credentials:
root/NcC@G#@8#?o!{c*
These IPs are likely associated with servers used for brute-force attacks or command-and-control (C2) infrastructure.
2. Chat Logs and Communication
Matrix Server:
matrix.bestflowers247.onlineThis appears to be the primary communication platform for BlackBasta members.
Chat IDs:
!nPsXVNwvPnfPbfsDcD:matrix.bestflowers247.online!kJVcUcyUsQhwBCuIPD:matrix.bestflowers247.online!AMKxwPhkMPYAfABhRo:matrix.bestflowers247.online
Usernames:
@lapa:matrix.bestflowers247.online@usernamegg:matrix.bestflowers247.online@usernameyy:matrix.bestflowers247.online@tinker:matrix.bestflowers247.online
3. Malicious Scripts and Tools
Script for Two Victims:
A script was shared in the chat logs, likely used for targeting two organizations.
Timestamp:
2024-04-11 20:35:46Sender:
@tinker:matrix.bestflowers247.onlineMessage: “вот скрипт на обе фирмы” (translation: “here is the script for both firms”).
4. Cryptocurrency Transactions
Bitcoin (BTC) Transactions:
Approximately 3 BTC was mentioned in a chat log, likely related to ransom payments or internal financial transactions.
The user
@usernameyy(Bio) mentioned being arrested and having their assets confiscated, including the 3 BTC.
5. Internal Group Dynamics
Key Members:
Lapa: One of the main administrators, responsible for managing brute-force attacks.
Cortes: Associated with the Qakbot group, had dealings with Americans, and distanced himself from attacks on Russian banks.
YY: Another administrator, heavily involved in support tasks and well-compensated.
Bio (Oleg Nefedov): Likely a high-ranking member, referred to as “Trump” in chat logs. Recently arrested, which caused concern among group members.
6. Attack Techniques
Brute-Force Attacks:
BlackBasta conducted brute-force attacks on the infrastructure of Russian banks under the administration of Lapa.
Example message: “жду тогда еще сервера для брута” (translation: “waiting for more servers for brute force”).
Use of VPNs and Proxies:
The group uses VPNs and proxies to mask their activities and avoid detection.
7. Internal Conflicts and Stress
Payment Disputes:
Members like Lapa are under significant stress due to their roles and receive less compensation compared to others.
Ransom payments are a key source of income for some members to support their families.
Leadership Issues:
The arrest of the group’s leader, Oleg Nefedov (referred to as “Trump”), has created risks for other members.
Internal conflicts over financial gains and operational decisions are evident.
8. Indicators of Internal Leaks
Data Leaks:
There are indications of internal leaks, with members pulling data systematically.
Concerns about who controls the data aggregation system, with suspicions of external interference (e.g., FBI).
Attack techniques and tools used by the Black Basta Group.
Summary of Tools and Techniques
Initial Access: Phishing, vulnerability exploitation.
Privilege Escalation: Mimikatz, scheduled tasks, registry manipulation.
Lateral Movement: RDP, Citrix, VPNs, proxies.
Data Exfiltration: Double extortion, FTP, SOCKS proxies.
Ransomware Deployment: Custom
.bastaransomware, encryption tools.Exploits: Microsoft Outlook RCE, Juniper SRX RCE, Windows 10 ASLR/DEP bypass.
Malware: Cobalt Strike, AgentTesla, Formbook, custom Python scripts.
Persistence: DLL injection, process hollowing, registry modifications.
Evasion: VPNs, proxies, code obfuscation.
Ransom Negotiation: Ransom notes, cryptocurrency payments.
Analysis
1. Initial Access
Phishing and Social Engineering:
Black Basta often gains initial access through phishing emails or social engineering tactics, tricking users into downloading malicious attachments or clicking on malicious links.
Exploitation of Vulnerabilities:
The group exploits known vulnerabilities in software and systems, such as Microsoft Exchange, VPNs, and RDP (Remote Desktop Protocol) services, to gain unauthorized access.
2. Privilege Escalation
Mimikatz:
Black Basta uses Mimikatz to extract credentials from the Local Security Authority Subsystem Service (LSASS) process, allowing them to escalate privileges and move laterally within the network.
Windows Scheduled Tasks and Registry Manipulation:
The group creates scheduled tasks or modifies the Windows registry to maintain persistence and ensure they can regain access even after initial removal attempts.
3. Lateral Movement
RDP and Citrix:
Black Basta leverages stolen credentials to establish RDP and Citrix sessions, enabling them to move laterally across internal networks and access critical systems.
VPN and Proxy Tunnels:
The group uses VPNs and SOCKS proxies to bypass firewalls and maintain secure communication channels within compromised networks.
4. Data Exfiltration
Double Extortion:
Before encrypting files, Black Basta exfiltrates sensitive data. They threaten to leak this data publicly if the ransom is not paid, adding pressure on victims.
FTP and SOCKS Proxies:
The group uses FTP and SOCKS proxies to transfer stolen data to external servers, ensuring anonymity and avoiding detection.
5. Ransomware Deployment
Black Basta Ransomware:
The group deploys its custom ransomware, which encrypts files on the target system and appends the
.bastaextension to encrypted files.Example: A malicious file named
e6393196-f020-4c2f-88fc-45ff7e22794f_encrypt_release_allsystem_x64.zipwas observed in their operations.
Encryption Tools:
The group uses custom encryption tools to lock files and demand ransom payments, typically in cryptocurrency (e.g., Bitcoin, Monero).
6. Exploits and Vulnerabilities
- They have been known to exploit vulnerabilities such as ConnectWise (CVE-2024-1709), ZeroLogon (CVE-2020-1472), NoPac (CVE-2021-42278andCVE-2021-42287), and PrintNightmare (CVE-2021-34527) to gain unauthorized access and escalate privileges within networks.
Microsoft Outlook Zero-Click RCE:
Black Basta exploits a zero-click vulnerability in Microsoft Outlook to execute malicious code without user interaction.
Juniper SRX Firewall RCE:
The group targets Juniper SRX firewalls using a zero-click exploit to gain unauthorized access to networks.
Windows 10 ASLR/DEP Bypass:
Black Basta bypasses Address Space Layout Randomization (ASLR) and Data Execution Prevention (DEP) protections in Windows 10 to execute remote code.
7. Malware and Tools
Cobalt Strike:
Black Basta uses Cobalt Strike for Command and Control (C2) communication, allowing them to manage compromised systems and execute commands remotely.
AgentTesla and Formbook:
These keyloggers and credential stealers are used to capture sensitive information, such as login credentials and financial data.
Custom Python Reverse Shell:
The group employs custom Python scripts to create reverse shells, enabling them to maintain remote control over compromised systems.
8. Persistence Mechanisms
DLL Injection and Process Hollowing:
Black Basta injects malicious code into legitimate processes (e.g.,
rundll32.exe) to avoid detection and maintain persistence.
Windows Registry Modifications:
The group modifies the Windows registry to ensure their malware runs automatically upon system startup.
9. Evasion Techniques
VPNs and Proxies:
Black Basta uses VPNs and proxies to mask their IP addresses and avoid detection by security tools.
Code Obfuscation:
The group obfuscates their malware code to evade detection by antivirus software and endpoint protection systems.
10. Ransom Negotiation
Ransom Notes:
Black Basta leaves ransom notes on infected systems, instructing victims on how to pay the ransom and receive decryption keys.
Cryptocurrency Payments:
The group demands ransom payments in cryptocurrencies like Bitcoin (BTC) and Monero (XMR) to ensure anonymity.
Process and Techniques for Demanding Ransom and Negotiating
Summary of Ransom Process
Initial Demand: High ransom amount with threats of data leakage.
Communication: Tor-based payment portal or encrypted chat.
Negotiation: Ransom amount can be reduced, with discounts for quick payment.
Payment: Cryptocurrency (Bitcoin or Monero) is required.
Decryption: Decryption key provided after payment, with possible manual intervention.
Threats: Data leak threats and countdown timers to pressure victims.
Post-Payment: Decryption assistance, but potential for follow-up attacks.
Analysis
1. Initial Ransom Demand
Ransom Note:
After encrypting the victim’s files, Black Basta leaves a ransom note on the infected system. This note typically includes:
Instructions on how to contact the group (usually via a Tor-based payment portal).
A deadline for payment, often with threats of data leakage if the ransom is not paid.
Details on the ransom amount, usually demanded in cryptocurrency (e.g., Bitcoin or Monero).
Double Extortion:
Black Basta exfiltrates sensitive data before encryption and threatens to leak it publicly if the ransom is not paid. This adds additional pressure on victims to comply.
2. Communication Channels
Tor Payment Portal:
Victims are directed to a Tor-based website where they can communicate with the attackers, negotiate the ransom, and make payments.
Encrypted Chat:
In some cases, Black Basta provides victims with access to an encrypted chat system to facilitate negotiations.
3. Ransom Amount
Initial Demand:
The initial ransom demand is often high, ranging from hundreds of thousands to millions of dollars, depending on the size and financial capacity of the victim.
Negotiation:
Black Basta is known to negotiate ransom amounts. Victims can often reduce the initial demand through negotiation, sometimes by as much as 50%.
Discounts for Quick Payment:
The group may offer discounts (e.g., 20%) for victims who pay quickly, typically within 48 hours.
4. Payment Methods
Cryptocurrency:
Black Basta demands payment in cryptocurrencies such as Bitcoin (BTC) and Monero (XMR) to ensure anonymity.
Wallet addresses are provided to victims for transferring the ransom.
Payment Proof:
Victims are required to provide proof of payment (e.g., transaction IDs) to receive the decryption key.
5. Decryption Process
Decryption Key:
After receiving the ransom, Black Basta provides a decryption key or tool to unlock the encrypted files.
In some cases, the group claims that the decryption process is automatic, but manual intervention may still be required.
Verification:
Victims are sometimes allowed to decrypt a small number of files as proof that the decryption key works before paying the full ransom.
6. Threats and Pressure Tactics
Data Leak Threats:
If the victim refuses to pay, Black Basta threatens to leak the stolen data on their dark web leak site. This can include sensitive business information, customer data, or intellectual property.
Countdown Timer:
Some victims report seeing a countdown timer on the ransom note or payment portal, adding urgency to the decision-making process.
7. Negotiation Tactics
Psychological Pressure:
Black Basta uses psychological tactics to pressure victims, such as emphasizing the potential damage from data leaks or the reputational harm of public exposure.
Flexibility in Negotiations:
The group is known to be flexible in negotiations, often reducing the ransom amount if the victim demonstrates an inability to pay the initial demand.
Multiple Rounds of Negotiation:
In some cases, negotiations may involve multiple rounds of back-and-forth communication, with the ransom amount being adjusted based on the victim’s responses.
8. Post-Payment Behavior
Decryption Assistance:
After payment, Black Basta typically provides the decryption key and instructions for recovering files. However, there have been reports of incomplete decryption or additional demands.
Follow-Up Attacks:
In some cases, the group may target the same victim again in the future, especially if they believe the victim is likely to pay again.
Internal Conflicts and Problems Within the Black Basta Group Over the Years
The Black Basta group, like many cybercriminal organizations, has faced internal conflicts and problems over the years. These issues often stem from disputes over financial distribution, leadership decisions, operational risks, and trust among members. Below is an analysis of the internal dynamics and conflicts within Black Basta
Summary of Internal Conflicts and Problems
Payment Disputes: Unequal compensation and delayed payments.
Leadership Conflicts: Power struggles and disagreements over decision-making.
Operational Stress: High-stress roles and burnout among members.
Trust Issues: Suspicion of moles and internal leaks.
Target Selection: Disagreements over risk vs. reward.
Technical Problems: Server reliability and code manipulation.
Financial and Legal Risks: Asset confiscation and legal exposure.
Recruitment Issues: Challenges in hiring and integrating new members.
Analysis
1. Disputes Over Payment and Profit Sharing
Unequal Compensation:
Members of Black Basta have reportedly expressed dissatisfaction with the distribution of profits. Some members, particularly those in technical or administrative roles, feel they are underpaid compared to others in the group.
For example, Lapa, one of the main administrators, is said to receive significantly less compensation despite handling critical tasks like brute-force attacks and infrastructure management.
Delayed Payments:
There have been instances where payments to members, especially those involved in coding and development, were delayed. This has led to frustration and disputes within the group.
2. Leadership Conflicts
Power Struggles:
Leadership disputes have arisen, particularly between high-ranking members like @usernamegg (a potential leader) and @nickolas. These conflicts often revolve around decision-making authority and operational control.
For instance, @nickolas has expressed a desire to exclude certain members from leadership roles, claiming they are not contributing enough. This has led to tensions within the group.
Arrest of Key Members:
The arrest of Oleg Nefedov (referred to as “Trump” within the group) created significant internal risks. His arrest not only disrupted operations but also raised concerns about the group’s exposure to law enforcement.
3. Operational Stress and Burnout
High-Stress Roles:
Members in critical roles, such as administrators and developers, often face high levels of stress due to the demanding nature of their tasks. For example, Lapa is described as being constantly busy with administrative duties and frequently criticized by superiors.
Lack of Work-Life Balance:
The pressure to maintain operational security and avoid detection has led to burnout among some members. This has resulted in decreased morale and productivity.
4. Trust Issues and Internal Leaks
Suspicion of Moles:
There have been concerns about the presence of “moles” or informants within the group. Members have questioned whether certain systems, such as their data aggregation tools, are being monitored by external entities like law enforcement.
For example, @nickolas has raised suspicions about data leaks, suggesting that some members may be systematically pulling data for unauthorized purposes.
Distrust Among Members:
Trust issues have arisen between key members, such as @usernamegg and @nickolas. @usernamegg has openly stated that he does not fully trust some members, leading to discussions about restricting access levels.
5. Disagreements Over Target Selection
Risk vs. Reward:
There have been disagreements over the selection of targets, particularly regarding the level of risk involved. For example, @usernamegg has expressed concerns about targeting large organizations, fearing increased scrutiny from law enforcement.
On the other hand, members like @n3auxaxl have argued that high-risk targets offer greater financial rewards, leading to internal debates about operational priorities.
6. Technical and Infrastructure Problems
Server Reliability:
The group has faced issues with the reliability of their server infrastructure. Members have debated whether to switch providers due to concerns about suspicious activity or potential compromises.
Code Manipulation:
There have been suspicions that changes were made to the group’s ransomware code, potentially to sabotage operations or expose members. This has led to internal investigations and further distrust.
7. Financial and Legal Risks
Asset Confiscation:
The arrest of key members has resulted in the confiscation of assets, including cryptocurrency and property. This has created financial strain and uncertainty within the group.
Legal Exposure:
The group’s operations have attracted significant attention from law enforcement agencies, increasing the risk of arrests and prosecutions. This has led to heightened paranoia and internal security measures.
8. Recruitment and Integration Issues
Hiring New Members:
The group has faced challenges in recruiting and integrating new members. Questions have been raised about the suitability of new recruits and their ability to contribute effectively.
For example, @usernamegg has expressed doubts about the hiring process, asking, “What exactly are we going to do? Is this person suitable for the team?”
