Ransomware protection includes technologies, strategies, and tools that can prevent cybercriminals from performing successful ransomware attacks. Ransomware attackers encrypt sensitive data and require organizations to pay a fee to regain access to their information assets.
Modern approaches to ransomware protection are very effective and straightforward to deploy. Sufficient ransomware protection starts with implementing basic security best practices such as strong authentication, malware protection, and network security measures. Organizations can build on this strong security posture by adding dedicated solutions to deter, prevent, and recover from ransomware attacks.
There are three types of solutions that can help protect against ransomware:
- Dedicated anti-ransomware solutions – several ransomware protection products are available, which can protect organizations at the network, file system, and application layer. These tools provide a multi-layered approach to stop ransomware from encrypting data.
- Operating system protections – some operating systems provide built-in protection against Ransomware. Most notably, from Windows 10, Microsoft provides ransomware protection built into the Windows Security command center.
- Decryptors – if you have already been hit by a ransomware attack, and there are no backups, it might still be possible to recover the files. Decryptors are available for some ransomware strains, and if you’re lucky, they might succeed in recovering your data.
How Does a Ransomware Attack Work?
-
- Ransomware encrypts files or locks the device—encryption involves scrambling files or a file structure until the data is no longer usable. Most ransomware programs use data encryption methods that victims cannot reverse without using a unique decryption key. This method enables attackers to demand ransom in exchange for a key.
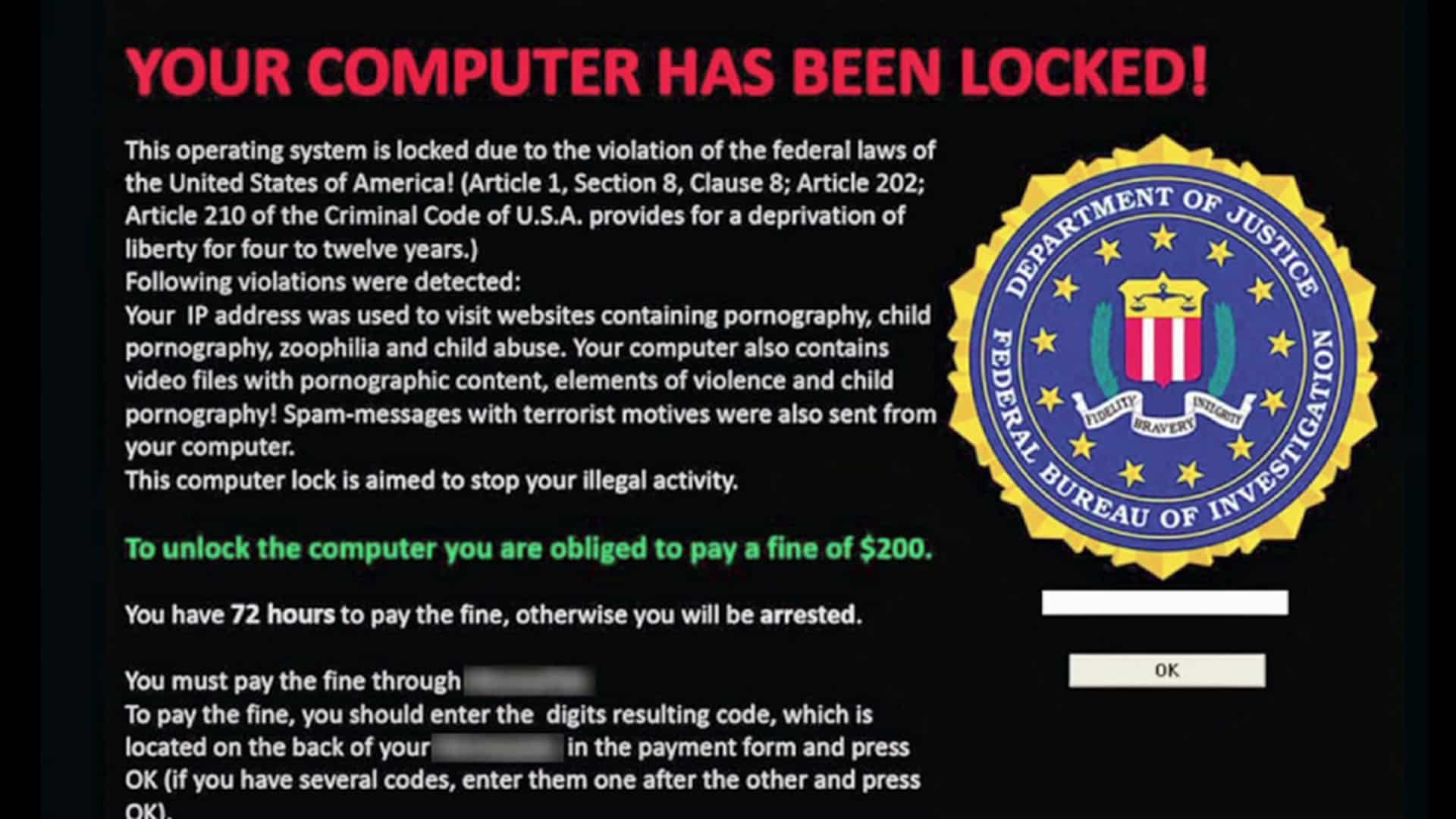
- A ransom note appears on the screen—once the ransomware encrypts the files. A note appears to specify a ransom demand, explaining the sum, mode of transfer, and deadline. Usually, attackers threaten that if victims do not meet the deadline, they will either increase the ransom, delete the files, or prevent any future attempt to decrypt them.
How Big Is the Ransomware Threat?
Ransomware is a global menace, threatening organizations of all sizes, and growing in scope and severity. Here are a few statistics that show the magnitude of the threat:
- How many are affected – according to a recent IDC report, 37% of organizations worldwide were the victim of a ransomware attack.
- Critical sectors targeted – The US Cybersecurity and Infrastructure Security Agency (CISA) reported there were ransomware attacks against 14 of 16 critical infrastructure sectors in the US
- Financial losses – according to the US Treasury’s Financial Crimes Enforcement Network (FinCEN), ransomware-related costs were $590 million in the first half of 2021, more than in the entire preceding year.
- Government involvement – Gartner predicts that by 2025, 30% of governments worldwide will have rules or regulations governing ransomware payments.
Tips From the Expert
In my experience, here are tips that can help you better enhance ransomware protection in your organization:
- Deploy application whitelisting for critical systems
Instead of relying solely on antivirus solutions, implement application whitelisting to allow only trusted software to run on critical systems. This prevents unauthorized software, like ransomware, from executing.
- Implement endpoint isolation featuresChoose EDR or MDR solutions that allow for automatic or manual isolation of endpoints during an attack. This feature quickly disconnects infected systems from the network, minimizing ransomware propagation.
- Use canary files to detect ransomware early
Place decoy (canary) files across your network that serve no business function. If these files are accessed or encrypted, it could indicate the presence of ransomware, triggering an immediate response.
- Implement file integrity monitoring
Continuously monitor files for unauthorized changes or deletions. Any unexpected alterations in sensitive files may signal the early stages of a ransomware attack, allowing you to respond before more damage is done.
- Develop a ransomware-specific incident response (IR) playbook
Create an IR playbook tailored specifically for ransomware attacks. It should include steps like identifying ransomware strains, disconnecting affected systems, and determining recovery paths, such as decryptors or clean backups.
These tips can help you deploy a proactive, layered defense against ransomware, ensuring quicker detection, containment, and recovery from potential attacks.

Eyal Gruner is the Co-Founder and CEO of Cynet. He is also Co-Founder and former CEO of BugSec, Israel’s leading cyber consultancy, and Versafe, acquired by F5 Networks. Gruner began his career at age 15 by hacking into his bank’s ATM to show the weakness of their security and has been recognized in Google’s security Hall of Fame.
Ransomware Protection Solutions
Dedicated Ransomware Protection Solutions
A dedicated security tool can provide holistic protection against ransomware, both at the network, file system, and application layer. One such solution is Cynet 360, an advanced threat detection and response platform that provides protection against threats, including ransomware, zero-day attacks, advanced persistent threats (APT), and trojans that can evade signature-based security measures.
-
- Pre-download—applies multiple mechanisms against exploits and fileless malware, which typically serves as a delivery method for the ransomware payload, preventing it from getting to the endpoint in the first place.
-
- Pre-execution prevention—applies machine-learning-based static analysis to identify ransomware patterns in binary files before they are executed.
- In runtime—employs behavioral analysis to identify ransomware-like behavior, and kill a process if it exhibits such behavior.
-
- Threat intelligence—uses a live feed comprising over 30 threat intelligence feeds to identify known ransomware.
-
- Fuzzy detection—employs a fuzzy hashing detection mechanism to detect automated variants of known ransomware.
-
- Sandbox—runs any loaded file in a sandbox and blocks execution upon identification of ransomware-like behavior.
-
- Decoy files—plants decoy data files on the hosts and applies a mechanism to ensure these are the first to be encrypted in a case of ransomware. Once Cynet detects that these files are going through encryption it kills the ransomware process.
- Propagation blocking—identifies the networking activity signature generated by hosts when ransomware is auto-propagating, and isolates the hosts from the network.
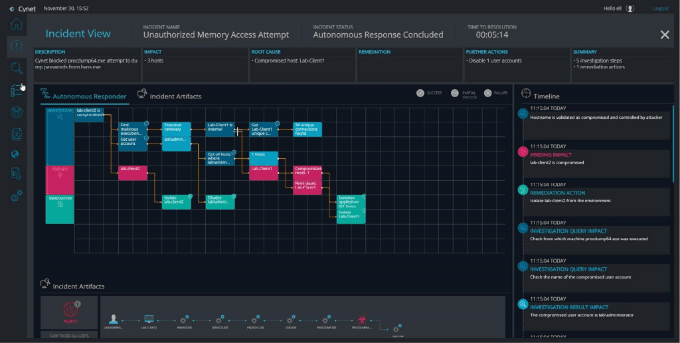
Cynet 360 provides all these anti-ransomware capabilities and more.
Windows 10 Ransomware Protection
The Windows operating system now has built-in ransomware protection, as part of Windows Security. This was introduced by Microsoft in Windows 10.
Windows 10 ransomware protection works by only allowing approved applications to make changes to the file system. This can prevent ransomware from encrypting files, but can also interfere with the operation of legitimate applications.
This is why ransomware protection is not enabled by default. To use it, you’ll need to enable it and configure it properly so that existing applications can continue functioning.
-
- Search for Windows Security in the Windows Start menu.
- In the Windows Security sidebar, select Virus & threat protection and click Manage ransomware protection.
- Switch the option Controlled folder access to On. This ensures only applications in the Windows Security allowlist can make changes to files on the operating system.
Decryptors
If a computing system is already infected by ransomware, files have been encrypted, and there are no backups, a last resort is to use decryptors.
There are a range of free decryption tools that are able to reverse the encryption by some types of ransomware. Be sure to use a legitimate descriptor from a source like the No More Ransom Project.
If there is a working decryptor for your ransomware, run it, obtain the key, and use it to decrypt the files. Note that depending on the type of ransomware and available system resources, this can take several hours.
- Identify ransomware type – before using a decryptor, identify the type of ransomware using Crypto Sheriff. You will need to provide the email address, Bitcoin account or web address shown in the ransomware message.
- Many ransomware types have no decryptor – in many cases there will be no working decryptor for the ransomware strain. In this case, consult with a security professional to see if there are additional ways to restore the files.
- Decryptors do not remove the ransomware – note that decryptors are not enough to clean a ransomware attack from your systems. Ransomware can activate secondary malware or delete your data. Make sure your system is clean from ransomware and all malware before using the decryptor.
What are the Most Dangerous Types of Ransomware?
Ryuk
Ryuk ransomware targets large, public-entity Windows systems. It works by encrypting data on an infected system and demanding ransom in Bitcoin. This ransomware appeared in 2018, initially believed to be of North Korean origin, but it is now suspected to be used by Russian criminal groups targeting organizations.
Sodinokibi
REvil/Sodinokibi ransomware encrypts files upon deployment and deletes the ransom request message after infection. The message demands bitcoin, notifying the victim that the demand will double if they do not pay the ransom on time.
REvil is delivered as Ransomware as a Service (RaaS), a model in which code authors develop the ransomware and affiliates spread it to collect the ransom. It was discovered in 2019 and has since become the 4th most distributed ransomware globally, targeting mostly European and American companies.
Netwalker
Netwalker ransomware holds its victim’s data hostage and leaks a sample of the stolen data online, threatening to release all the data to the dark web if the victim does not pay the ransom on time. It was created in 2019 by Circus Spider, a cybercrime group, and later shifted to a RaaS model to operate on a larger scale. It often spreads through phishing emails.
Maze
Maze is a Windows ransomware developed as a variant of ChaCha ransomware. It targets organizations worldwide, demanding a cryptocurrency payment in exchange for the encrypted data, threatening to leak the victim’s confidential data if they refuse to pay.
- Spam emails, typically through malicious links or attachments like Word or Excel files.
- RDP brute force attacks.
- An exploit kit.
- Through the victim’s client or partner who has already fallen victim to the attack.
CryptoWall
CryptoWall ransomware encrypts files and their names and demands a ransom for a decryption key. It typically spreads by phishing and spam emails, hacked websites, malicious ads, or other malware. Cryptowall uses a Trojan horse to deliver malicious payloads. By encrypting file names, CryptoWall increases the pressure on victims, who consequently pay the ransom to get their data back.
Locky
Locky ransomware encrypts important files on an infected computer, holding them hostage, delivering a ransom note that demands payment in exchange for the encrypted files. It typically arrived as an email including a Word doc attachment containing the code. Locky was discovered in 2016 and became a significant threat. While Locky is currently out of commission, other variants have emerged.
Cerber
Cerber is delivered as RaaS providing attacker licenses that split the ransom between the developer and affiliates. Cerber affiliates can deliver Cerber ransomware to various targets in return for providing the author with 40% of the ransom. The author creates the ransomware in this exchange, and affiliates find targets to distribute it.
9 Ransomware Prevention Tips
Here are several ways you can prevent ransomware from striking your organization.
- Actively manage access – restrict access to known users and known legitimate traffic to safeguard your data and applications from encryption. Strong passwords and multi-factor authentication provide added security to prevent bad actors from accessing your systems
- Centralized management – to deal with the complete range of ransomware threats, organizations must use centralized management procedures and systems. Sensitive information should be categorized, assessed, and properly secured wherever it resides.
- Use anti-malware solutions – block suspicious executable files, and leverage email security solutions to monitor email traffic for malicious messages and block phishing attacks. To address unknown and zero-day malware, including zero-day ransomware, use advanced security technology such as signatureless behavioral analysis.
- Implement centralized patch management – patch all endpoints when vulnerabilities are identified, including operating systems, mobile devices, applications, cloud resources, software, and IoT.
- Protect backup repositories – implement the 3-2-1 rule by keeping three copies of your information, storing it on two distinct media types, and keeping one of these media off-site. It is also important to periodically test backups to ensure they are functional and maintain data integrity.
- Educate users – Help your end users by providing them with the practice and education they need to protect against ransomware attacks. Consistent communication and awareness training will let everyone in your organization know the threat of ransomware and gain familiarity with security approaches. Ensure that your employees know how to report suspicious behavior and understand the importance of timely reporting.
- Establish a disaster recovery plan – to ensure they can completely recover data and applications in case of disaster, organizations must create, test, and uphold practices, tools, and procedures for business continuity and disaster recovery (BCDR).
- Conduct a risk assessment – categorize types of ransomware disasters and create priorities for business continuity and recovery.
- Create an incident response plan – the plan should clarify what to do in the case of a ransomware attack, including determining data sensitivity and disconnecting affected systems from the network to contain the attack.